Cyber Security
Increase your sleep score and let us deliver a comprehensive security solution to help you protect your business

Many businesses aren’t prepared when it comes to the security of their IT systems. Unfortunately, security breaches are all too common and can have devastating effects on a business. On average, one in five SMBs report that they’ve fallen victim to a ransomware attack. Downtime costs are up by 200% year over year, and the cost of downtime is 23 times greater than the average ransom requested in 2020.
Putting in the extra time and effort to focus solely on security might be overwhelming for business owners. However, partnering with an MSP can help you simplify the process and minimize stress while improving your overall security and compliance posture. Contact us now to schedule a security consultation.
Data Pros Security Solutions provide the foundation that SMBs need to effectively meet their security needs. The solution combines intelligent profiling and alerting technology with support from our Security Operations Center (SOC) facility.
- Firewall and Network Security
- Endpoint Security and Antivirus
- Risk Assessments
- Email and Web Security
- Information Protection
- Security Awareness Training
- Dark Web Monitoring
- Help Desk Remediation
Download our security best practices checklist for working remotely

The Cost of Cleanup
Security, Compliance & Identity, Microsoft
As a Microsoft partner, we can enhance your organization’s security with Microsoft 365, a complete, intelligent solution including Office 365, Windows 11, and Enterprise Mobility + Security that empowers everyone to be creative and work together, securely. Learn more about the power of Microsoft Defender by reading our blog and visiting our Microsoft Security web page.

Drowning in data? Dashboards are your lifeline
Your business generates massive amounts of data, but is any of it actually helping you? Without the right tools, raw data is just noise. Business

Why small businesses are struggling with cybersecurity
Cybersecurity has become a priority for businesses of all sizes, not just big corporations. Small businesses, often overlooked in the cybersecurity conversation, are now prime
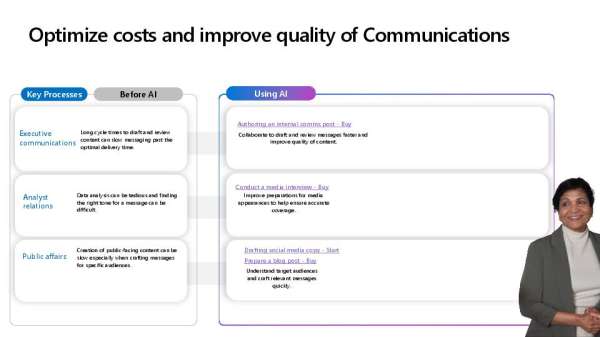
Using Copilot to Optimize Communication Costs & Quality
Your communications team faces constant pressure to do more with less — balancing budgets while improving engagement. @Microsoft Copilot is here to help reduce communication costs and enhance message quality with AI-powered efficiencies. 📈 See how #AI is reshaping communications in this insightful infographic.